 |
|
Please Whitelist This Site?
I know everyone hates ads. But please understand that I am providing premium content for free that takes hundreds of hours of time to research and write. I don't want to go to a pay-only model like some sites, but when more and more people block ads, I end up working for free. And I have a family to support, just like you. :)
If you like The TCP/IP Guide, please consider the download version. It's priced very economically and you can read all of it in a convenient format without ads.
If you want to use this site for free, I'd be grateful if you could add the site to the whitelist for Adblock. To do so, just open the Adblock menu and select "Disable on tcpipguide.com". Or go to the Tools menu and select "Adblock Plus Preferences...". Then click "Add Filter..." at the bottom, and add this string: "@@||tcpipguide.com^$document". Then just click OK.
Thanks for your understanding!
Sincerely, Charles Kozierok
Author and Publisher, The TCP/IP Guide
|
|
|

Custom Search
|
|
PPP Authentication Protocols: Password Authentication Protocol (PAP) and Challenge Handshake Authentication Protocol (CHAP)
(Page 2 of 3)
Password Authentication Protocol (PAP).
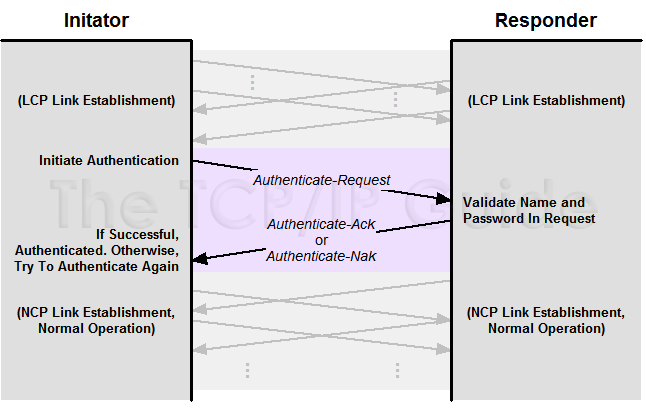
PAP is a very straight-forward authentication scheme, consisting of only two basic steps, as shown in Figure 29:
- Authentication Request: The
initiating device sends an Authenticate-Request message that
contains a name and a password.
- Authentication Reply: The responding
device looks at the name and password and decides whether to accept
the initiating device and continue in setting up the link. If so, it
sends back an Authenticate-Ack. Otherwise, it sends an Authenticate-Nak.
Figure 29: PPP Password Authentication Protocol (PAP) Authentication
PAP works using a simple exchange of a request containing name and password information, and a reply indicating whether or not authentication was successful.
Simple. Now, remember what Einstein said about simplicity? PAP is another example of something that is just too simple for its own good. Chief amongst its flaws is that it transmits the user name and password in clear text across the link. This is a big “no-no” in security protocols, as it means any eavesdropper can get the password and use it in the future. PAP also provides no protection against various security attacks. For example, an unauthorized user could simply try different passwords indefinitely and hope he or she eventually found one that worked. PAP also puts control of the authentication squarely on the shoulders of the initiating device (usually a client machine) which is not considered desirable.
|
| |||||||||||||||||||
Home - Table Of Contents - Contact Us
The TCP/IP Guide (http://www.TCPIPGuide.com)
Version 3.0 - Version Date: September 20, 2005
© Copyright 2001-2005 Charles M. Kozierok. All Rights Reserved.
Not responsible for any loss resulting from the use of this site.






