 |
|
Please Whitelist This Site?
I know everyone hates ads. But please understand that I am providing premium content for free that takes hundreds of hours of time to research and write. I don't want to go to a pay-only model like some sites, but when more and more people block ads, I end up working for free. And I have a family to support, just like you. :)
If you like The TCP/IP Guide, please consider the download version. It's priced very economically and you can read all of it in a convenient format without ads.
If you want to use this site for free, I'd be grateful if you could add the site to the whitelist for Adblock. To do so, just open the Adblock menu and select "Disable on tcpipguide.com". Or go to the Tools menu and select "Adblock Plus Preferences...". Then click "Add Filter..." at the bottom, and add this string: "@@||tcpipguide.com^$document". Then just click OK.
Thanks for your understanding!
Sincerely, Charles Kozierok
Author and Publisher, The TCP/IP Guide
|
|
|

Custom Search
|
|
PPP Link Control Protocol (LCP)
(Page 2 of 3)
LCP Link Configuration
Link configuration is arguably the most important job that LCP does in PPP. During the Link Establishment phase, LCP frames are exchanged that enable the two physically-connected devices to negotiate the conditions under which the link will operate. Figure 27 shows the entire procedure, which we will now examine in detail.
The process starts with the initiating device (let's call it device A, yeah, isn't that original) creating a Configure-Request frame that contains a variable number of configuration options that it wants to see set up on the link. This is basically device A's “wish list” for how it wants the link created.
|
The main PPP document (RFC 1661) defines a number of different configuration options that the initiator can specify in this request. Any one of these can be included and if so, filled in with the value corresponding to what device A wants for that option. If absent, this means device A is neither requesting nor specifying that option. The six options are:
- Maximum-Receive-Unit (MRU): Lets
device A specify the maximum size datagram it wants the link
to be able to carry.
- Authentication-Protocol: Device
A can indicate the type of authentication protocol it wishes
to use (if any).
- Quality-Protocol: If device A
wants to enable quality monitoring on the link, what protocol to use
(though there is only one currently defined: LQR).
- Magic-Number: Used to detect looped
back links or other anomalies in the connection.
- Protocol-Field-Compression: Allows
device A to specify that it wants to use “compressed”
(8 bit) Protocol fields in PPP data frames instead of the normal
16 bit Protocol field. This provides a small but free savings
(one byte) on each PPP frame. Note that this has nothing to do with
the compression feature offered by CCP. See the PPP general frame format
topic for more on this feature.
- Address-and-Control-Field-Compression (ACFC): The same as the option just above but used to compress the Address and Control fields, again for small bandwidth savings. Again, see the PPP general frame format topic for more.
Other options may also be added to this list by optional feature protocols. For example, Multilink PPP adds several options that must be negotiated during link setup.
The other device (let's call it say… device B J) receives the Configure-Request and processes it. It then has three choices of how to respond:
- If every option in it is acceptable
in every way, device B sends back a Configure-Ack (“acknowledge”).
The negotiation is complete.
- If all the options that device A
sent are valid ones that device B recognizes and is capable of
negotiating, but it doesn't accept the values device A sent,
then device B returns a Configure-Nak (“negative
acknowledge”) frame. This message includes a copy of each configuration
option that B found unacceptable.
- If any of the options that A sent were either unrecognized by B, or represent ways of using the link that B considers not only unacceptable but not even subject to negotiation, it returns a Configure-Reject containing each of the objectionable options.
The difference between a Configure-Nak and a Configure-Reject is that the former is like device B saying “I don't accept your terms, but I'm willing to haggle”, while the latter is device B basically saying “No way Jose”. For example, if device A tries to request PAP as the authentication protocol but device B wants to use CHAP, it will send a Configure-Nak. If device B doesn't support authentication at all, it will send a Configure-Reject.
|
|
| |||||||||||||||||||
Home - Table Of Contents - Contact Us
The TCP/IP Guide (http://www.TCPIPGuide.com)
Version 3.0 - Version Date: September 20, 2005
© Copyright 2001-2005 Charles M. Kozierok. All Rights Reserved.
Not responsible for any loss resulting from the use of this site.







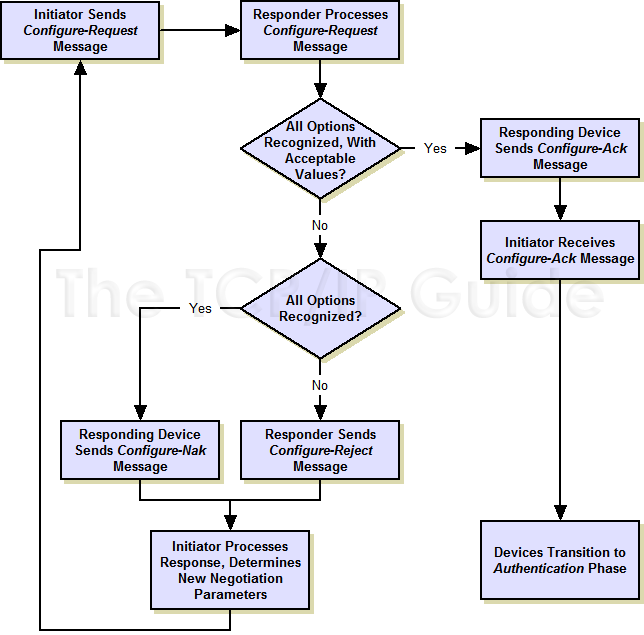
 Note: Even after receiving a reject, device A can retry the negotiation with a new Configure-Request.
Note: Even after receiving a reject, device A can retry the negotiation with a new Configure-Request.